ms-chap authentification failed: возможные причины
Здравствуйте, товарищи!
Есть вопрос к клиентам компании "Транс телеком", использующим для выхода в Интернет ОС Gnu/Linux.
Какие в принципе возможны причины указанной ошибки? Ну, разумеется, за исключением таких очевидных глупостей, как пустой счёт и неправильно введённый логин/пароль.
Используется Ubuntu 10.04.
Спасибо!
Есть вопрос к клиентам компании "Транс телеком", использующим для выхода в Интернет ОС Gnu/Linux.
Какие в принципе возможны причины указанной ошибки? Ну, разумеется, за исключением таких очевидных глупостей, как пустой счёт и неправильно введённый логин/пароль.
Используется Ubuntu 10.04.
Спасибо!
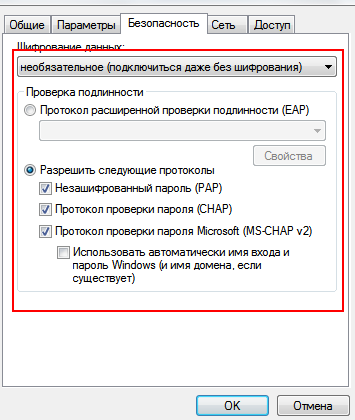
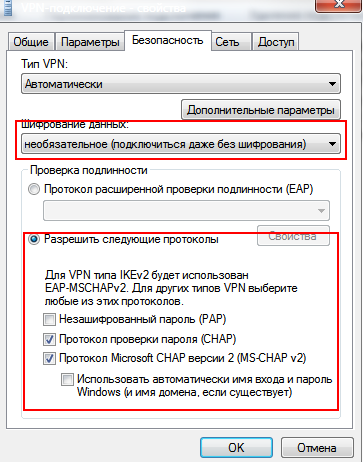
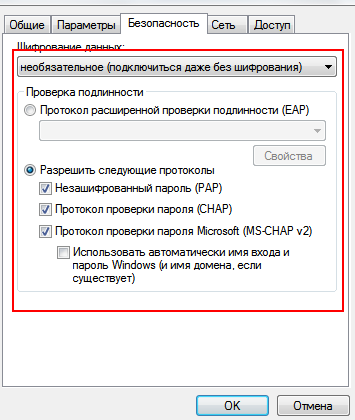
тип шифрования
А разве кроме MD5 может быть что-то ещё?
Вот эти параметры имел ввиду (к сожалению нет ща линухи под рукой скрины сделать )
vpn
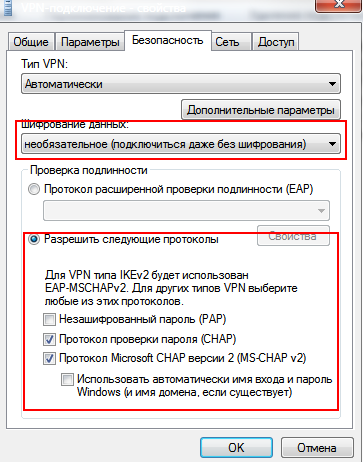
ppoe
P.S. md5 - не шифрование, а хеширование
vpn
ppoe
P.S. md5 - не шифрование, а хеширование
Это всё замечательно. Ну, а в Linux-то , всё-таки, куда копать?
начните с /etc/ppp, какие у вас там файлы, какое содержимое?
Простой способ: Настрой подключение через графический network-manager, там всё это быстрее настраивается чем конфигами.
Второй способ - хз как ты настраивал проверь в /etc/ppp/peers/твое_подключение параметры
refuse/require-pap
refuse/require-mschap
refuse/require-chap
Второй способ - хз как ты настраивал проверь в /etc/ppp/peers/твое_подключение параметры
refuse/require-pap
refuse/require-mschap
refuse/require-chap
Использую утилиту pppoeconf.
Мои конфиги имеют такой вид:
/etc/network/interfaces
auto lo
iface lo inet loopback
auto eth0
iface eth0 inet dhcp
auto dsl-provider
iface dsl-provider inet ppp
pre-up /sbin/ifconfig eth0 up # line maintained by pppoeconf
provider dsl-provider
/etc/ppp/options
# /etc/ppp/options
#
# Originally created by Jim Knoble <jmknoble@mercury.interpath.net>
# Modified for Debian by alvar Bray <alvar@meiko.co.uk>
# Modified for PPP Server setup by Christoph Lameter <clameter@debian.org>
#
# To quickly see what options are active in this file, use this command:
# egrep -v '#|^ *$' /etc/ppp/options
# Specify which DNS Servers the incoming Win95 or WinNT Connection should use
# Two Servers can be remotely configured
# ms-dns 192.168.1.1
# ms-dns 192.168.1.2
# Specify which WINS Servers the incoming connection Win95 or WinNT should use
# ms-wins 192.168.1.50
# ms-wins 192.168.1.51
# Run the executable or shell command specified after pppd has
# terminated the link. This script could, for example, issue commands
# to the modem to cause it to hang up if hardware modem control signals
# were not available.
#disconnect "chat -- \d+++\d\c OK ath0 OK"
# async character map -- 32-bit hex; each bit is a character
# that needs to be escaped for pppd to receive it. 0x00000001
# represents '\x01', and 0x80000000 represents '\x1f'.
asyncmap 0
# Require the peer to authenticate itself before allowing network
# packets to be sent or received.
# Please do not disable this setting. It is expected to be standard in
# future releases of pppd. Use the call option (see manpage) to disable
# authentication for specific peers.
#auth
noauth
# ... Unfortunately, fixing this properly in the peers file
# (/etc/ppp/peers/ppp0, typically) is apparently incompatible with the
# paradigm used by gnome-system-tools and system-tools-backend for
# managing the peers files. So in Ubuntu Feisty we change the default.
# Use hardware flow control (i.e. RTS/CTS) to control the flow of data
# on the serial port.
crtscts
# Use software flow control (i.e. XON/XOFF) to control the flow of data
# on the serial port.
#xonxoff
# Specifies that certain characters should be escaped on transmission
# (regardless of whether the peer requests them to be escaped with its
# async control character map). The characters to be escaped are
# specified as a list of hex numbers separated by commas. Note that
# almost any character can be specified for the escape option, unlike
# the asyncmap option which only allows control characters to be
# specified. The characters which may not be escaped are those with hex
# values 0x20 - 0x3f or 0x5e.
#escape 11,13,ff
# Don't use the modem control lines.
#local
# Specifies that pppd should use a UUCP-style lock on the serial device
# to ensure exclusive access to the device.
lock
# Don't show the passwords when logging the contents of PAP packets.
# This is the default.
hide-password
# When logging the contents of PAP packets, this option causes pppd to
# show the password string in the log message.
#show-password
# Use the modem control lines. On Ultrix, this option implies hardware
# flow control, as for the crtscts option. (This option is not fully
# implemented.)
modem
# Set the MRU [Maximum Receive Unit] value to <n> for negotiation. pppd
# will ask the peer to send packets of no more than <n> bytes. The
# minimum MRU value is 128. The default MRU value is 1500. A value of
# 296 is recommended for slow links (40 bytes for TCP/IP header + 256
# bytes of data).
#mru 542
# Set the interface netmask to <n>, a 32 bit netmask in "decimal dot"
# notation (e.g. 255.255.255.0).
#netmask 255.255.255.0
# Disables the default behaviour when no local IP address is specified,
# which is to determine (if possible) the local IP address from the
# hostname. With this option, the peer will have to supply the local IP
# address during IPCP negotiation (unless it specified explicitly on the
# command line or in an options file).
#noipdefault
# Enables the "passive" option in the LCP. With this option, pppd will
# attempt to initiate a connection; if no reply is received from the
# peer, pppd will then just wait passively for a valid LCP packet from
# the peer (instead of exiting, as it does without this option).
#passive
# With this option, pppd will not transmit LCP packets to initiate a
# connection until a valid LCP packet is received from the peer (as for
# the "passive" option with old versions of pppd).
#silent
# Don't request or allow negotiation of any options for LCP and IPCP
# (use default values).
#-all
# Disable Address/Control compression negotiation (use default, i.e.
# address/control field disabled).
#-ac
# Disable asyncmap negotiation (use the default asyncmap, i.e. escape
# all control characters).
#-am
# Don't fork to become a background process (otherwise pppd will do so
# if a serial device is specified).
#-detach
# Disable IP address negotiation (with this option, the remote IP
# address must be specified with an option on the command line or in
# an options file).
#-ip
# Disable IPCP negotiation and IP communication. This option should
# only be required if the peer is buggy and gets confused by requests
# from pppd for IPCP negotiation.
#noip
# Disable magic number negotiation. With this option, pppd cannot
# detect a looped-back line.
#-mn
# Disable MRU [Maximum Receive Unit] negotiation (use default, i.e.
# 1500).
#-mru
# Disable protocol field compression negotiation (use default, i.e.
# protocol field compression disabled).
#-pc
# Require the peer to authenticate itself using PAP.
#+pap
# Don't agree to authenticate using PAP.
#-pap
# Require the peer to authenticate itself using CHAP [Cryptographic
# Handshake Authentication Protocol] authentication.
#+chap
# Don't agree to authenticate using CHAP.
#-chap
# Disable negotiation of Van Jacobson style IP header compression (use
# default, i.e. no compression).
#-vj
# Increase debugging level (same as -d). If this option is given, pppd
# will log the contents of all control packets sent or received in a
# readable form. The packets are logged through syslog with facility
# daemon and level debug. This information can be directed to a file by
# setting up /etc/syslog.conf appropriately (see syslog.conf(5)). (If
# pppd is compiled with extra debugging enabled, it will log messages
# using facility local2 instead of daemon).
#debug
# Append the domain name <d> to the local host name for authentication
# purposes. For example, if gethostname() returns the name porsche,
# but the fully qualified domain name is porsche.Quotron.COM, you would
# use the domain option to set the domain name to Quotron.COM.
#domain <d>
# Enable debugging code in the kernel-level PPP driver. The argument n
# is a number which is the sum of the following values: 1 to enable
# general debug messages, 2 to request that the contents of received
# packets be printed, and 4 to request that the contents of transmitted
# packets be printed.
#kdebug n
# Set the MTU [Maximum Transmit Unit] value to <n>. Unless the peer
# requests a smaller value via MRU negotiation, pppd will request that
# the kernel networking code send data packets of no more than n bytes
# through the PPP network interface.
#mtu <n>
# Set the name of the local system for authentication purposes to <n>.
# This is a privileged option. With this option, pppd will use lines in the
# secrets files which have <n> as the second field when looking for a
# secret to use in authenticating the peer. In addition, unless overridden
# with the user option, <n> will be used as the name to send to the peer
# when authenticating the local system to the peer. (Note that pppd does
# not append the domain name to <n>.)
#name <n>
# Enforce the use of the hostname as the name of the local system for
# authentication purposes (overrides the name option).
#usehostname
# Set the assumed name of the remote system for authentication purposes
# to <n>.
#remotename <n>
# Add an entry to this system's ARP [Address Resolution Protocol]
# table with the IP address of the peer and the Ethernet address of this
# system.
proxyarp
# Use the system password database for authenticating the peer using
# PAP. Note: mgetty already provides this option. If this is specified
# then dialin from users using a script under Linux to fire up ppp wont work.
# login
# If this option is given, pppd will send an LCP echo-request frame to the
# peer every n seconds. Normally the peer should respond to the echo-request
# by sending an echo-reply. This option can be used with the
# lcp-echo-failure option to detect that the peer is no longer connected.
lcp-echo-interval 30
# If this option is given, pppd will presume the peer to be dead if n
# LCP echo-requests are sent without receiving a valid LCP echo-reply.
# If this happens, pppd will terminate the connection. Use of this
# option requires a non-zero value for the lcp-echo-interval parameter.
# This option can be used to enable pppd to terminate after the physical
# connection has been broken (e.g., the modem has hung up) in
# situations where no hardware modem control lines are available.
lcp-echo-failure 4
# Set the LCP restart interval (retransmission timeout) to <n> seconds
# (default 3).
#lcp-restart <n>
# Set the maximum number of LCP terminate-request transmissions to <n>
# (default 3).
#lcp-max-terminate <n>
# Set the maximum number of LCP configure-request transmissions to <n>
# (default 10).
#lcp-max-configure <n>
# Set the maximum number of LCP configure-NAKs returned before starting
# to send configure-Rejects instead to <n> (default 10).
#lcp-max-failure <n>
# Set the IPCP restart interval (retransmission timeout) to <n>
# seconds (default 3).
#ipcp-restart <n>
# Set the maximum number of IPCP terminate-request transmissions to <n>
# (default 3).
#ipcp-max-terminate <n>
# Set the maximum number of IPCP configure-request transmissions to <n>
# (default 10).
#ipcp-max-configure <n>
# Set the maximum number of IPCP configure-NAKs returned before starting
# to send configure-Rejects instead to <n> (default 10).
#ipcp-max-failure <n>
# Set the PAP restart interval (retransmission timeout) to <n> seconds
# (default 3).
#pap-restart <n>
# Set the maximum number of PAP authenticate-request transmissions to
# <n> (default 10).
#pap-max-authreq <n>
# Set the maximum time that pppd will wait for the peer to authenticate
# itself with PAP to <n> seconds (0 means no limit).
#pap-timeout <n>
# Set the CHAP restart interval (retransmission timeout for
# challenges) to <n> seconds (default 3).
#chap-restart <n>
# Set the maximum number of CHAP challenge transmissions to <n>
# (default 10).
#chap-max-challenge
# If this option is given, pppd will rechallenge the peer every <n>
# seconds.
#chap-interval <n>
# With this option, pppd will accept the peer's idea of our local IP
# address, even if the local IP address was specified in an option.
#ipcp-accept-local
# With this option, pppd will accept the peer's idea of its (remote) IP
# address, even if the remote IP address was specified in an option.
#ipcp-accept-remote
# Disable the IPXCP and IPX protocols.
# To let pppd pass IPX packets comment this out --- you'll probably also
# want to install ipxripd, and have the Internal IPX Network option enabled
# in your kernel. /usr/doc/HOWTO/IPX-HOWTO.gz contains more info.
noipx
# Exit once a connection has been made and terminated. This is the default,
# unless the `persist' or `demand' option has been specified.
#nopersist
# Do not exit after a connection is terminated; instead try to reopen
# the connection.
#persist
# Terminate after n consecutive failed connection attempts.
# A value of 0 means no limit. The default value is 10.
#maxfail <n>
# Initiate the link only on demand, i.e. when data traffic is present.
# With this option, the remote IP address must be specified by the user on
# the command line or in an options file. Pppd will initially configure
# the interface and enable it for IP traffic without connecting to the peer.
# When traffic is available, pppd will connect to the peer and perform
# negotiation, authentication, etc. When this is completed, pppd will
# commence passing data packets (i.e., IP packets) across the link.
#demand
# Specifies that pppd should disconnect if the link is idle for <n> seconds.
# The link is idle when no data packets (i.e. IP packets) are being sent or
# received. Note: it is not advisable to use this option with the persist
# option without the demand option. If the active-filter option is given,
# data packets which are rejected by the specified activity filter also
# count as the link being idle.
#idle <n>
# Specifies how many seconds to wait before re-initiating the link after
# it terminates. This option only has any effect if the persist or demand
# option is used. The holdoff period is not applied if the link was
# terminated because it was idle.
#holdoff <n>
# Wait for up n milliseconds after the connect script finishes for a valid
# PPP packet from the peer. At the end of this time, or when a valid PPP
# packet is received from the peer, pppd will commence negotiation by
# sending its first LCP packet. The default value is 1000 (1 second).
# This wait period only applies if the connect or pty option is used.
#connect-delay <n>
# Packet filtering: for more information, see pppd(8)
# Any packets matching the filter expression will be interpreted as link
# activity, and will cause a "demand" connection to be activated, and reset
# the idle connection timer. (idle option)
# The filter expression is akin to that of tcpdump(1)
#active-filter <filter-expression>
# ---<End of File>---
/etc/ppp/peers/dsl-provider
# Minimalistic default options file for DSL/PPPoE connections
noipdefault
defaultroute
replacedefaultroute
hide-password
#lcp-echo-interval 30
#lcp-echo-failure 4
noauth
persist
#mtu 1492
#persist
#maxfail 0
#holdoff 20
plugin rp-pppoe.so eth0
user "username524104796"
usepeerdns
В итоге в логе имею вот это:
Feb 7 15:40:17 vova-desktop pppd[15253]: Plugin rp-pppoe.so loaded.
Feb 7 15:40:17 vova-desktop pppd[15255]: pppd 2.4.4 started by root, uid 0
Feb 7 15:40:17 vova-desktop pppd[15255]: PPP session is 55094
Feb 7 15:40:17 vova-desktop pppd[15255]: Using interface ppp0
Feb 7 15:40:17 vova-desktop pppd[15255]: Connect: ppp0 <--> eth0
Feb 7 15:40:19 vova-desktop pppd[15255]: MS-CHAP authentication failed: E=691 Authentication failure
Feb 7 15:40:19 vova-desktop pppd[15255]: CHAP authentication failed
Да и ещё: я тут в порыве экспериментирования успел, со времени моего первого поста, снести Ubuntu 10.04 и поставить 8.04, однако, думаю это, в данном случае, не принципиально, так как результат всё равно такой же, стало быть дело не в номере релиза.
Мои конфиги имеют такой вид:
/etc/network/interfaces
auto lo
iface lo inet loopback
auto eth0
iface eth0 inet dhcp
auto dsl-provider
iface dsl-provider inet ppp
pre-up /sbin/ifconfig eth0 up # line maintained by pppoeconf
provider dsl-provider
/etc/ppp/options
# /etc/ppp/options
#
# Originally created by Jim Knoble <jmknoble@mercury.interpath.net>
# Modified for Debian by alvar Bray <alvar@meiko.co.uk>
# Modified for PPP Server setup by Christoph Lameter <clameter@debian.org>
#
# To quickly see what options are active in this file, use this command:
# egrep -v '#|^ *$' /etc/ppp/options
# Specify which DNS Servers the incoming Win95 or WinNT Connection should use
# Two Servers can be remotely configured
# ms-dns 192.168.1.1
# ms-dns 192.168.1.2
# Specify which WINS Servers the incoming connection Win95 or WinNT should use
# ms-wins 192.168.1.50
# ms-wins 192.168.1.51
# Run the executable or shell command specified after pppd has
# terminated the link. This script could, for example, issue commands
# to the modem to cause it to hang up if hardware modem control signals
# were not available.
#disconnect "chat -- \d+++\d\c OK ath0 OK"
# async character map -- 32-bit hex; each bit is a character
# that needs to be escaped for pppd to receive it. 0x00000001
# represents '\x01', and 0x80000000 represents '\x1f'.
asyncmap 0
# Require the peer to authenticate itself before allowing network
# packets to be sent or received.
# Please do not disable this setting. It is expected to be standard in
# future releases of pppd. Use the call option (see manpage) to disable
# authentication for specific peers.
#auth
noauth
# ... Unfortunately, fixing this properly in the peers file
# (/etc/ppp/peers/ppp0, typically) is apparently incompatible with the
# paradigm used by gnome-system-tools and system-tools-backend for
# managing the peers files. So in Ubuntu Feisty we change the default.
# Use hardware flow control (i.e. RTS/CTS) to control the flow of data
# on the serial port.
crtscts
# Use software flow control (i.e. XON/XOFF) to control the flow of data
# on the serial port.
#xonxoff
# Specifies that certain characters should be escaped on transmission
# (regardless of whether the peer requests them to be escaped with its
# async control character map). The characters to be escaped are
# specified as a list of hex numbers separated by commas. Note that
# almost any character can be specified for the escape option, unlike
# the asyncmap option which only allows control characters to be
# specified. The characters which may not be escaped are those with hex
# values 0x20 - 0x3f or 0x5e.
#escape 11,13,ff
# Don't use the modem control lines.
#local
# Specifies that pppd should use a UUCP-style lock on the serial device
# to ensure exclusive access to the device.
lock
# Don't show the passwords when logging the contents of PAP packets.
# This is the default.
hide-password
# When logging the contents of PAP packets, this option causes pppd to
# show the password string in the log message.
#show-password
# Use the modem control lines. On Ultrix, this option implies hardware
# flow control, as for the crtscts option. (This option is not fully
# implemented.)
modem
# Set the MRU [Maximum Receive Unit] value to <n> for negotiation. pppd
# will ask the peer to send packets of no more than <n> bytes. The
# minimum MRU value is 128. The default MRU value is 1500. A value of
# 296 is recommended for slow links (40 bytes for TCP/IP header + 256
# bytes of data).
#mru 542
# Set the interface netmask to <n>, a 32 bit netmask in "decimal dot"
# notation (e.g. 255.255.255.0).
#netmask 255.255.255.0
# Disables the default behaviour when no local IP address is specified,
# which is to determine (if possible) the local IP address from the
# hostname. With this option, the peer will have to supply the local IP
# address during IPCP negotiation (unless it specified explicitly on the
# command line or in an options file).
#noipdefault
# Enables the "passive" option in the LCP. With this option, pppd will
# attempt to initiate a connection; if no reply is received from the
# peer, pppd will then just wait passively for a valid LCP packet from
# the peer (instead of exiting, as it does without this option).
#passive
# With this option, pppd will not transmit LCP packets to initiate a
# connection until a valid LCP packet is received from the peer (as for
# the "passive" option with old versions of pppd).
#silent
# Don't request or allow negotiation of any options for LCP and IPCP
# (use default values).
#-all
# Disable Address/Control compression negotiation (use default, i.e.
# address/control field disabled).
#-ac
# Disable asyncmap negotiation (use the default asyncmap, i.e. escape
# all control characters).
#-am
# Don't fork to become a background process (otherwise pppd will do so
# if a serial device is specified).
#-detach
# Disable IP address negotiation (with this option, the remote IP
# address must be specified with an option on the command line or in
# an options file).
#-ip
# Disable IPCP negotiation and IP communication. This option should
# only be required if the peer is buggy and gets confused by requests
# from pppd for IPCP negotiation.
#noip
# Disable magic number negotiation. With this option, pppd cannot
# detect a looped-back line.
#-mn
# Disable MRU [Maximum Receive Unit] negotiation (use default, i.e.
# 1500).
#-mru
# Disable protocol field compression negotiation (use default, i.e.
# protocol field compression disabled).
#-pc
# Require the peer to authenticate itself using PAP.
#+pap
# Don't agree to authenticate using PAP.
#-pap
# Require the peer to authenticate itself using CHAP [Cryptographic
# Handshake Authentication Protocol] authentication.
#+chap
# Don't agree to authenticate using CHAP.
#-chap
# Disable negotiation of Van Jacobson style IP header compression (use
# default, i.e. no compression).
#-vj
# Increase debugging level (same as -d). If this option is given, pppd
# will log the contents of all control packets sent or received in a
# readable form. The packets are logged through syslog with facility
# daemon and level debug. This information can be directed to a file by
# setting up /etc/syslog.conf appropriately (see syslog.conf(5)). (If
# pppd is compiled with extra debugging enabled, it will log messages
# using facility local2 instead of daemon).
#debug
# Append the domain name <d> to the local host name for authentication
# purposes. For example, if gethostname() returns the name porsche,
# but the fully qualified domain name is porsche.Quotron.COM, you would
# use the domain option to set the domain name to Quotron.COM.
#domain <d>
# Enable debugging code in the kernel-level PPP driver. The argument n
# is a number which is the sum of the following values: 1 to enable
# general debug messages, 2 to request that the contents of received
# packets be printed, and 4 to request that the contents of transmitted
# packets be printed.
#kdebug n
# Set the MTU [Maximum Transmit Unit] value to <n>. Unless the peer
# requests a smaller value via MRU negotiation, pppd will request that
# the kernel networking code send data packets of no more than n bytes
# through the PPP network interface.
#mtu <n>
# Set the name of the local system for authentication purposes to <n>.
# This is a privileged option. With this option, pppd will use lines in the
# secrets files which have <n> as the second field when looking for a
# secret to use in authenticating the peer. In addition, unless overridden
# with the user option, <n> will be used as the name to send to the peer
# when authenticating the local system to the peer. (Note that pppd does
# not append the domain name to <n>.)
#name <n>
# Enforce the use of the hostname as the name of the local system for
# authentication purposes (overrides the name option).
#usehostname
# Set the assumed name of the remote system for authentication purposes
# to <n>.
#remotename <n>
# Add an entry to this system's ARP [Address Resolution Protocol]
# table with the IP address of the peer and the Ethernet address of this
# system.
proxyarp
# Use the system password database for authenticating the peer using
# PAP. Note: mgetty already provides this option. If this is specified
# then dialin from users using a script under Linux to fire up ppp wont work.
# login
# If this option is given, pppd will send an LCP echo-request frame to the
# peer every n seconds. Normally the peer should respond to the echo-request
# by sending an echo-reply. This option can be used with the
# lcp-echo-failure option to detect that the peer is no longer connected.
lcp-echo-interval 30
# If this option is given, pppd will presume the peer to be dead if n
# LCP echo-requests are sent without receiving a valid LCP echo-reply.
# If this happens, pppd will terminate the connection. Use of this
# option requires a non-zero value for the lcp-echo-interval parameter.
# This option can be used to enable pppd to terminate after the physical
# connection has been broken (e.g., the modem has hung up) in
# situations where no hardware modem control lines are available.
lcp-echo-failure 4
# Set the LCP restart interval (retransmission timeout) to <n> seconds
# (default 3).
#lcp-restart <n>
# Set the maximum number of LCP terminate-request transmissions to <n>
# (default 3).
#lcp-max-terminate <n>
# Set the maximum number of LCP configure-request transmissions to <n>
# (default 10).
#lcp-max-configure <n>
# Set the maximum number of LCP configure-NAKs returned before starting
# to send configure-Rejects instead to <n> (default 10).
#lcp-max-failure <n>
# Set the IPCP restart interval (retransmission timeout) to <n>
# seconds (default 3).
#ipcp-restart <n>
# Set the maximum number of IPCP terminate-request transmissions to <n>
# (default 3).
#ipcp-max-terminate <n>
# Set the maximum number of IPCP configure-request transmissions to <n>
# (default 10).
#ipcp-max-configure <n>
# Set the maximum number of IPCP configure-NAKs returned before starting
# to send configure-Rejects instead to <n> (default 10).
#ipcp-max-failure <n>
# Set the PAP restart interval (retransmission timeout) to <n> seconds
# (default 3).
#pap-restart <n>
# Set the maximum number of PAP authenticate-request transmissions to
# <n> (default 10).
#pap-max-authreq <n>
# Set the maximum time that pppd will wait for the peer to authenticate
# itself with PAP to <n> seconds (0 means no limit).
#pap-timeout <n>
# Set the CHAP restart interval (retransmission timeout for
# challenges) to <n> seconds (default 3).
#chap-restart <n>
# Set the maximum number of CHAP challenge transmissions to <n>
# (default 10).
#chap-max-challenge
# If this option is given, pppd will rechallenge the peer every <n>
# seconds.
#chap-interval <n>
# With this option, pppd will accept the peer's idea of our local IP
# address, even if the local IP address was specified in an option.
#ipcp-accept-local
# With this option, pppd will accept the peer's idea of its (remote) IP
# address, even if the remote IP address was specified in an option.
#ipcp-accept-remote
# Disable the IPXCP and IPX protocols.
# To let pppd pass IPX packets comment this out --- you'll probably also
# want to install ipxripd, and have the Internal IPX Network option enabled
# in your kernel. /usr/doc/HOWTO/IPX-HOWTO.gz contains more info.
noipx
# Exit once a connection has been made and terminated. This is the default,
# unless the `persist' or `demand' option has been specified.
#nopersist
# Do not exit after a connection is terminated; instead try to reopen
# the connection.
#persist
# Terminate after n consecutive failed connection attempts.
# A value of 0 means no limit. The default value is 10.
#maxfail <n>
# Initiate the link only on demand, i.e. when data traffic is present.
# With this option, the remote IP address must be specified by the user on
# the command line or in an options file. Pppd will initially configure
# the interface and enable it for IP traffic without connecting to the peer.
# When traffic is available, pppd will connect to the peer and perform
# negotiation, authentication, etc. When this is completed, pppd will
# commence passing data packets (i.e., IP packets) across the link.
#demand
# Specifies that pppd should disconnect if the link is idle for <n> seconds.
# The link is idle when no data packets (i.e. IP packets) are being sent or
# received. Note: it is not advisable to use this option with the persist
# option without the demand option. If the active-filter option is given,
# data packets which are rejected by the specified activity filter also
# count as the link being idle.
#idle <n>
# Specifies how many seconds to wait before re-initiating the link after
# it terminates. This option only has any effect if the persist or demand
# option is used. The holdoff period is not applied if the link was
# terminated because it was idle.
#holdoff <n>
# Wait for up n milliseconds after the connect script finishes for a valid
# PPP packet from the peer. At the end of this time, or when a valid PPP
# packet is received from the peer, pppd will commence negotiation by
# sending its first LCP packet. The default value is 1000 (1 second).
# This wait period only applies if the connect or pty option is used.
#connect-delay <n>
# Packet filtering: for more information, see pppd(8)
# Any packets matching the filter expression will be interpreted as link
# activity, and will cause a "demand" connection to be activated, and reset
# the idle connection timer. (idle option)
# The filter expression is akin to that of tcpdump(1)
#active-filter <filter-expression>
# ---<End of File>---
/etc/ppp/peers/dsl-provider
# Minimalistic default options file for DSL/PPPoE connections
noipdefault
defaultroute
replacedefaultroute
hide-password
#lcp-echo-interval 30
#lcp-echo-failure 4
noauth
persist
#mtu 1492
#persist
#maxfail 0
#holdoff 20
plugin rp-pppoe.so eth0
user "username524104796"
usepeerdns
В итоге в логе имею вот это:
Feb 7 15:40:17 vova-desktop pppd[15253]: Plugin rp-pppoe.so loaded.
Feb 7 15:40:17 vova-desktop pppd[15255]: pppd 2.4.4 started by root, uid 0
Feb 7 15:40:17 vova-desktop pppd[15255]: PPP session is 55094
Feb 7 15:40:17 vova-desktop pppd[15255]: Using interface ppp0
Feb 7 15:40:17 vova-desktop pppd[15255]: Connect: ppp0 <--> eth0
Feb 7 15:40:19 vova-desktop pppd[15255]: MS-CHAP authentication failed: E=691 Authentication failure
Feb 7 15:40:19 vova-desktop pppd[15255]: CHAP authentication failed
Да и ещё: я тут в порыве экспериментирования успел, со времени моего первого поста, снести Ubuntu 10.04 и поставить 8.04, однако, думаю это, в данном случае, не принципиально, так как результат всё равно такой же, стало быть дело не в номере релиза.
Обратите внимание! Вам постом выше уже ответили.
В первую очередь играться флагами
refuse-pap
refuse-eap
refuse-chap
refuse-mschap
require-mschap-v2
require-mppe-128
для справки по флагам : man pppd
В первую очередь играться флагами
refuse-pap
refuse-eap
refuse-chap
refuse-mschap
require-mschap-v2
require-mppe-128
для справки по флагам : man pppd
А ещё вот что настораживает: по команде
пишет вот такие нехорошие слова:
А зачем тогда написано вот это?
Код:
sudo /etc/init.d/networking/restart
Код:
dsl-provider:ERROR while getting interface flags: No such device
Код:
auto dsl-provider
iface dsl-provider inet ppp
pre-up /sbin/ifconfig eth0 up # line maintained by pppoeconf
provider dsl-provider
iface dsl-provider inet ppp
pre-up /sbin/ifconfig eth0 up # line maintained by pppoeconf
provider dsl-provider
